Protect your surveys from participants displaying high-risk or abnormal behaviors.
Suspicious Users is a targeted security feature designed to block participants whose behavior indicates potential fraud risk - before they enter your survey. By flagging participants who exhibit unusual or technically suspicious traits, dtect helps protect your data quality while giving you full control over which behaviors are acceptable for your project.
Key Benefits
-
Fraud Prevention: Blocks participants flagged for abnormal device or browser characteristics
-
Customizable Control: Select which behaviors are suspicious for each project
-
Real-time Screening: Flags suspicious behavior instantly after participant consent
How It Works
Suspicious Users is triggered immediately after the participant clicks "I Agree" on the survey entry page. dtect collects technical metadata from the participant's environment. This includes device settings, network characteristics, and browser configurations.
Each project can have specific suspicious signals enabled. If a participant matches any of the selected suspicious behaviors, they are instantly terminated and returned to their supplier with a Security Terminate status.
If no flagged behaviors are detected, the participant continues to the next stage of dtect's security checks.
Suspicious Signals Available
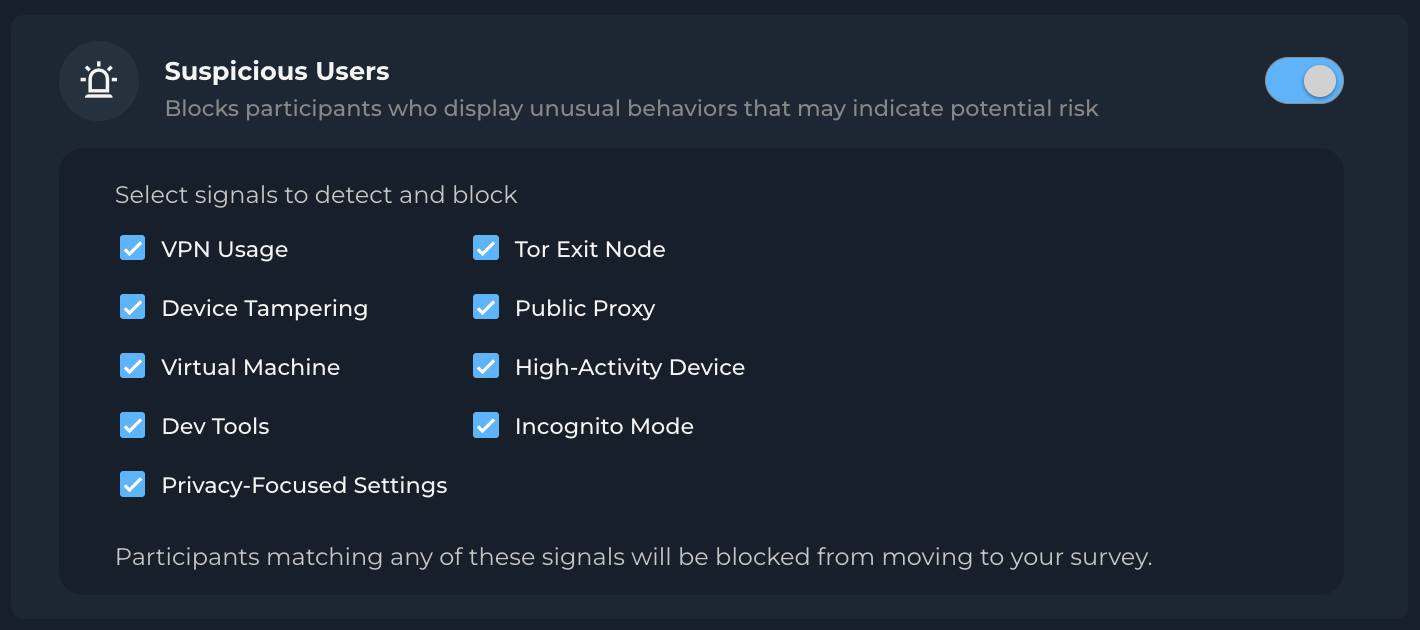
When enabling Suspicious Users, you can choose which of the following signals to consider suspicious:
-
Privacy-Focused Settings
-
Tor Exit Node
-
Public Proxy
-
High-Activity Device
-
Incognito Detection
-
VPN Detection
-
Tampering Detection
-
Virtual Machine Detection
-
Dev Tools Detection
These options allow you to fine-tune your security settings to suit your audience. For example, disabling VPN Detection may be appropriate when targeting frequent travelers or IT professionals.
Technical Overview
-
Data Collection: dtectcollects environmental data post-consent.
-
Evaluation Logic: If any selected signal returns
true, the participant is terminated. -
Security Routing: Failed participants are redirected to the project's Security Terminate Redirect.
-
Status Tagging:
-
dtect Status:security_terminate -
dtect Status Description:Suspicious Users -
Suspicious Behavior:failorpass -
Suspicious Users Check Results: signal-by-signal pass/fail (e.g.,vpnResult: true,incognito: false)
-
Monitoring and Results
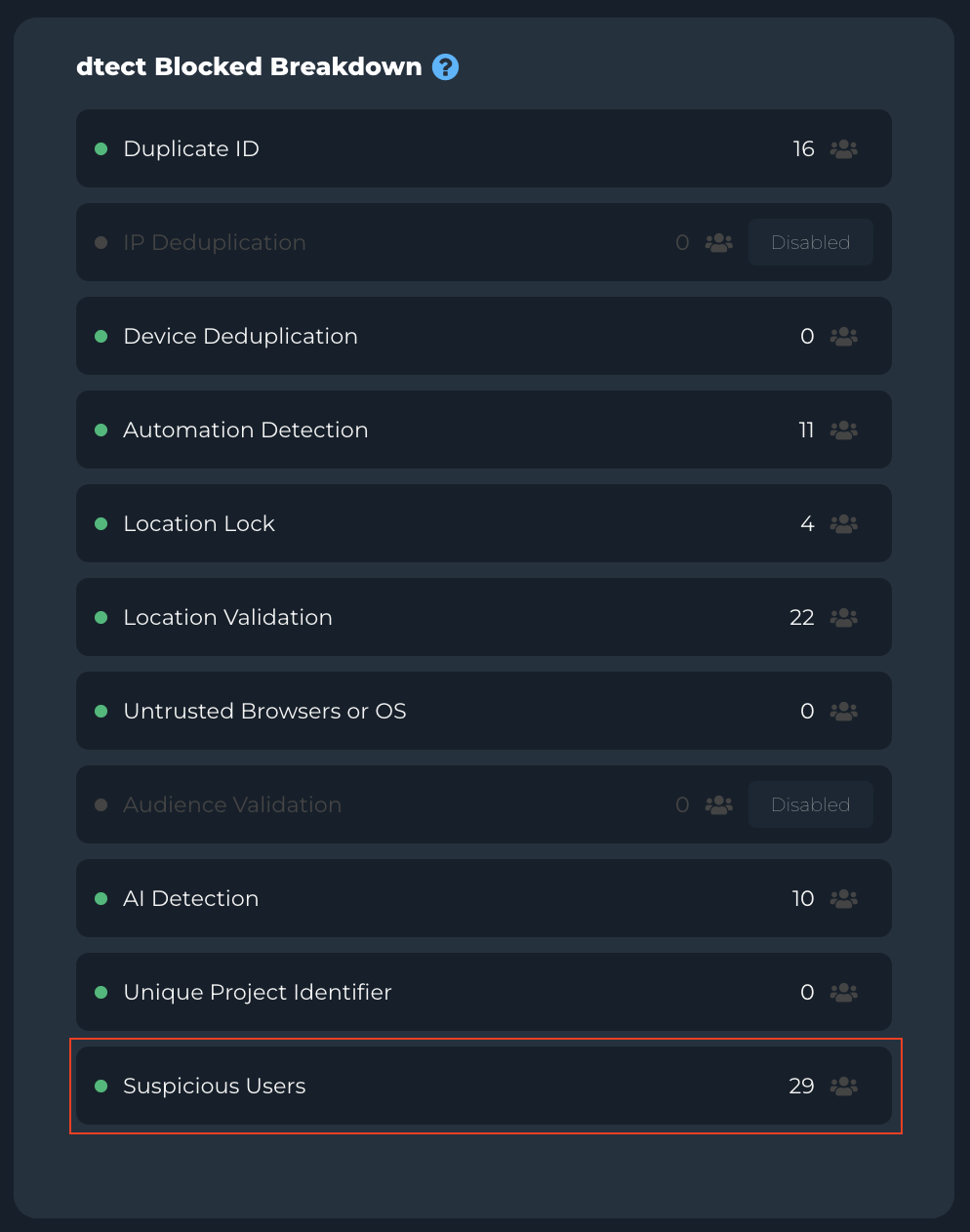
On the Progress tab, platform users can easily monitor how many participants were terminated by Suspicious Users:
-
Visual indicators highlight Suspicious User blocks
-
CSV exports include granular details on flagged behaviors per participant
📁 Export Columns Include:
-
Suspicious Behavior -
Suspicious Users Check Results -
Full list of signal results (e.g.,
virtualMachine: true)
Considerations & Best Practices
While highly effective in filtering out fraudulent behavior, Suspicious Users has the possibility to occasionally block legitimate respondents---particularly in more technical or privacy-conscious audiences.
🔍 Example: When targeting IT professionals or digital nomads, it may be wise to disable "Incognito" and/or "VPN Detection."
📊 Product Insight: Typically fewer than 6% of total participants are flagged by one or more Suspicious Users signals---making it a low-impact, high-precision security tool.
The most effective implementation uses Suspicious Users alongside other core features like Location Validation and Automation Detection to balance security with accessibility.
Troubleshooting Scenarios
| Issue | Suggested Action |
|---|---|
| High Termination Rates | Review selected suspicious signals; consider relaxing for tech-savvy audiences |
| Unexpected Participant Blocks | Cross-check exported results in the Progress tab for specific triggers |
| International Studies | Consider disabling VPN or Proxy detection if targeting regions with high usage |
Need Help?
Contact your Customer Success Manager for:
-
Signal-specific recommendations
-
Audience-specific configuration strategies
-
Security termination analysis and optimization tips
Suspicious Users helps prevent bad data from reaching your survey---before it becomes a problem. Combine it with other dtect security tools for comprehensive protection.