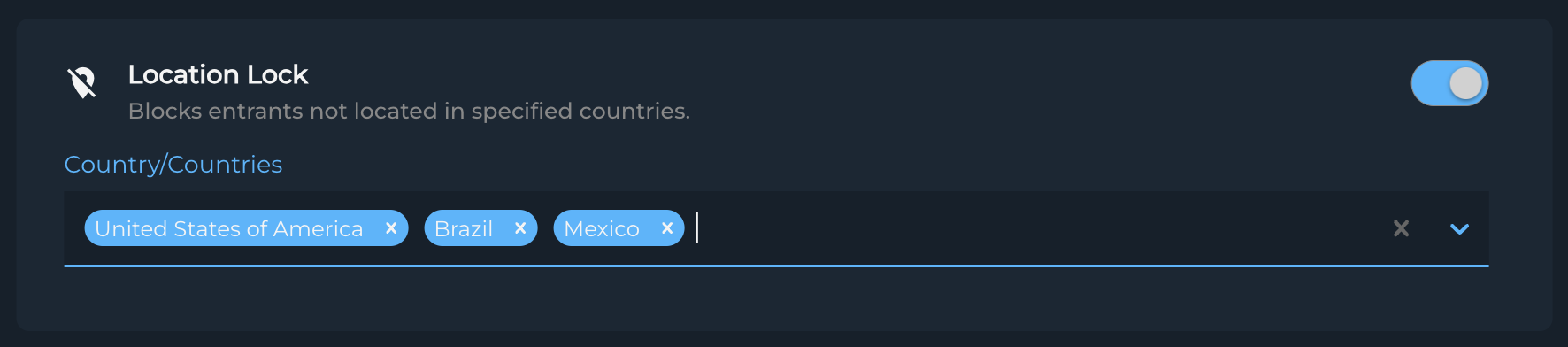
Location Lock ensures your survey data comes exclusively from your targeted geographical regions by preventing access from non-approved countries. This feature is essential for maintaining regional relevance and meeting geographical compliance requirements.
Location Lock works best when configured at the start of your project. Adding countries later won't affect previously blocked participant
Key Benefits
- Geographic Compliance: Ensures participants only come from approved regions
- Data Accuracy: Maintains regional relevance of your research
- Simplified Screening: Reduces the need for additional geographic screening questions
How It Works
- Define allowed countries during project setup
- Participants from non-approved countries are automatically blocked
- Security Terminate status is assigned to blocked participants
When participants are blocked by Location Lock, they receive a security terminate status without impacting your survey quotas or incurring charges.
Using Location Lock Effectively
When to Enable
- Region-specific research projects
- Studies with geographic compliance requirements
- Multi-country studies with specific target markets
Consider enabling both Location Lock and Location Validation for maximum geographic security, especially in studies where participant location is crucial.
Configuration Tips
-
Country Selection
- Select all relevant countries for your study
- Include any secondary markets if applicable
- Consider adding backup countries for quota management
-
Project Planning
- Set up country restrictions before launching
- Account for multi-language requirements
- Consider regional internet infrastructure
Save commonly used country combinations as templates for future projects to ensure consistency across similar studies.
Troubleshooting
Common Scenarios
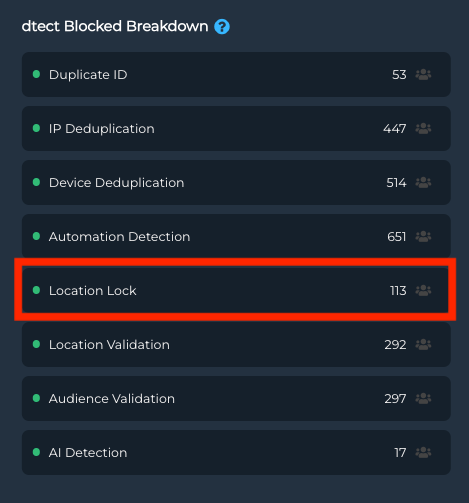
High Security Termination Rates
- Verify selected countries match target audience
- Check supplier targeting settings
- Review geographic distribution of terminations
📊 Analysis Tip
A spike in security terminations might indicate supplier targeting issues rather than Location Lock configuration problems.
Missing Valid Participants
- Confirm all target countries are included
- Check for recent country list updates
- Verify supplier geographic targeting
Best Practices
Effective Location Lock implementation typically results in consistent security termination rates across similar projects targeting the same regions
-
Implementation
- Define clear geographic requirements
- Include all necessary countries
- Test configuration before full launch
-
Monitoring
- Track security termination rates
- Watch for unusual patterns
-
Optimization
- Regular review of country settings
- Adjust based on project needs
- Coordinate with supplier targeting
Special Considerations
For projects targeting specific regions within countries, combine Location Lock with additional screening questions for precise geographic targeting.
Multi-Country Studies
- Enable appropriate languages
- Consider time zone differences
- Account for regional holidays
Regional Compliance
- Review local data collection laws
- Consider privacy regulations
- Document geographic restrictions
Questions or Concerns?
Contact your Customer Success Manager for:
- Country selection guidance
- Implementation strategies
- Compliance recommendations
💫 Customer Success
"dtect has given us peace of mind that the quality of our online samples meets our standards while at the same time being a cost-effective field management tool." - William Bickford, Source Global Research
Remember: Location Lock is your first line of defense for geographic targeting. Combine it with other security features for a comprehensive approach to data quality.